Business Card Fraud Protection: 10 Best Practices

Your field supervisor calls from the job site. Someone used the company card at a gas station 300 miles away while the card was supposedly locked in the truck. By the time you discover the fraud, multiple unauthorized charges have already hit your account.
For project-based businesses with distributed teams, this scenario plays out constantly. Field workers operate outside your security perimeter, and cards travel between job sites without centralized oversight.
The math is brutal. Only 22% of organizations recover 75% or more of fraud losses. These 12 best practices will help you establish the controls needed to protect your distributed workforce.
1. Set Granular Spending Limits by Role and Project
Every card should have transaction-level, daily, and monthly limits tied to the cardholder's actual purchasing authority. For field laborers, set transaction limits at $100-$500. Crew leads handling equipment rentals need $500-$2,000. Site supervisors managing lodging and meals can go higher.
When limits are too restrictive, employees find creative workarounds. When limits are too loose, you lose visibility until the statement arrives.
Modern corporate charge cards take this further. With Engine X, you set daily, weekly, and monthly limits by employee, project, or expense type, and those limits refresh automatically. A $75/day limit means your crew member can only spend $75 today and gets a fresh $75 tomorrow. You don’t have to worry about someone burning through the weekly budget by Wednesday.
2. Enforce Authorization Levels Through Technology
Manual approval processes create delays that fraudsters exploit. Technology-enforced segregation of duties eliminates these gaps.
Three critical separations must exist:
- Card custody: Field workers hold cards. Finance controls issuance. No one person both issues and uses cards.
- Transaction authorization: Project managers authorize routine purchases. Finance approves exceptions.
- Recording: A separate team handles GL coding. Purchasers cannot code their own expenses.
Generic business cards from traditional banks give you none of this. A standard Amex or Chase card offers broad acceptance and basic rewards, but zero project-based controls, no category restrictions by employee, and no way to enforce spending rules before the charge happens.
Corporate charge cards built for operational businesses change this equation. With Engine X, you issue unlimited physical and virtual cards to your team, each with spending controls by employee or expense type — plus daily, weekly, and monthly limits.
Category restrictions let you limit a card to fuel-only or lodging-only purchases. And because every transaction flows into the same dashboard as your travel bookings, finance gets a single view of all spending without chasing down individual cardholders.
3. Implement Tiered Approval Workflows
These thresholds should match your typical project sizes and spending patterns.

Configure your system to auto-reject transactions that exceed thresholds without proper approvals. When a $3,000 charge attempts processing with only project manager approval, the system blocks it. No manual intervention needed.
4. Deploy Real-Time Transaction Monitoring
Traditional corporate card programs rely on monthly reconciliation. It’s a black hole where fraud hides for 30 days. You discover unauthorized charges when the statement arrives, long after the damage is done.
Real-time monitoring alerts your team within seconds, letting you freeze the card before the next charge hits.
Modern platforms use AI-powered monitoring that detects policy violations before reimbursement processing occurs. These systems evaluate transaction attributes in real time, including amount patterns, geographic location, device fingerprinting, and merchant categories.
When your Houston crew's card suddenly processes a charge in Miami during a weekend, the system flags it immediately.
This is where expense management platforms fall short for project-based businesses. They offer solid expense automation and policy controls, but their rewards are generic (typically 1-1.5%). They lack travel-specific controls, and employees still pay out of pocket before getting reimbursed.
For companies whose crews live in hotels and work across multiple job sites, that model creates both fraud exposure and cash flow problems.
5. Train Field Workers on Fraud Recognition
Training must be mobile-first for distributed workforces. 30 minutes of foundational content broken into 5-10 minute microlearning segments works best.
Your training program should cover these essential topics:
- Recognizing phishing and BEC schemes targeting field employees
- Proper card storage and immediate loss reporting procedures
- Emergency card deactivation procedures with 24/7 contact mechanisms
Phishing attacks targeting field workers often impersonate vendors requesting "updated payment information" or fake HR emails about expense policy changes. Train workers to verify any payment-related request through a known phone number, not the one in the suspicious email.
BEC schemes have evolved, with fraudsters researching company org charts to impersonate executives convincingly. Regular reinforcement keeps these threats top of mind.
6. Document Clear Usage Policies with Consequences
Policy language must be specific. For example, "Corporate cards may be used ONLY for pre-approved business expenses. Violations, including transaction splitting or falsified documentation, will result in immediate card revocation and disciplinary action up to termination."
Clear consequences matter because the alternative is costly.
In a documented case, the Jacksonville Jaguars lost $22 million from virtual card misuse due to inadequate oversight.
7. Conduct Regular Security Audits
Continuous automated monitoring forms your first tier. Monthly audits should sample at least 10% of transactions from each cardholder.
Flag any receipts that are photocopies, missing timestamps, or have altered amounts. Cross-reference vendor names against your approved vendor list.
Monthly detailed reviews examine:
- Receipt completeness and authenticity
- Transactions near policy limits
- Round-number patterns
- Vendor concentration by employee
- Approval chain validation
Watch for behavioral red flags: employees living beyond apparent means, unusually close vendor relationships, and refusal to take vacations.
K&K Electric lived this reconciliation nightmare firsthand. Their team spent 2+ hours every Monday booking rooms, sending credit card authorization forms, and hoping hotels received them, then spent the end of every week reconciling charges and matching folios to individual employees.
That fragmented process meant fraud or errors could hide for days before anyone noticed. After switching to Engine, they cut 30 hours per month from booking and reconciliation, consolidating the visibility that makes regular audits actually effective.
8. Prioritize EMV, Tokenization, and Virtual Cards
EMV chip technology achieved an 80% decrease in card-present fraud globally. Tokenization reduces card-not-present fraud by up to 34% by replacing actual card numbers with tokens that have no exploitable value if stolen.
Virtual cards eliminate physical card risk entirely. Issue a unique number for each vendor or project with preset spending limits and automatic expiration dates. For construction companies managing multiple job sites, each project gets its own card number with specific limits—no more shared cards passing between crews.
Traditional business cards from banks like Amex or Chase offer no virtual card issuance and no way to tie limits to specific projects. Expense management platforms like Brex and Ramp offer virtual cards but lack travel-specific controls.
Engine X solves both problems: unlimited physical and virtual cards with instant issuance, each tied to customizable spend controls by employee, project, or expense type. Earn up to 10% back on Engine travel and 1.5% on everything else1, with no annual fee2.
9. Implement Two-Factor Authentication on All Card Portals
Two-factor (multi-factor) authentication can prevent the vast majority of password-related account compromises. Microsoft analysis cited by OWASP suggests it would have stopped 99.9% of account compromises from attacks like brute-force, credential stuffing, and password spraying. Use app-based authenticators rather than SMS, which is vulnerable to SIM swapping.
10. Establish and Rehearse Incident Response Protocols
Card networks mandate specific reporting timelines:
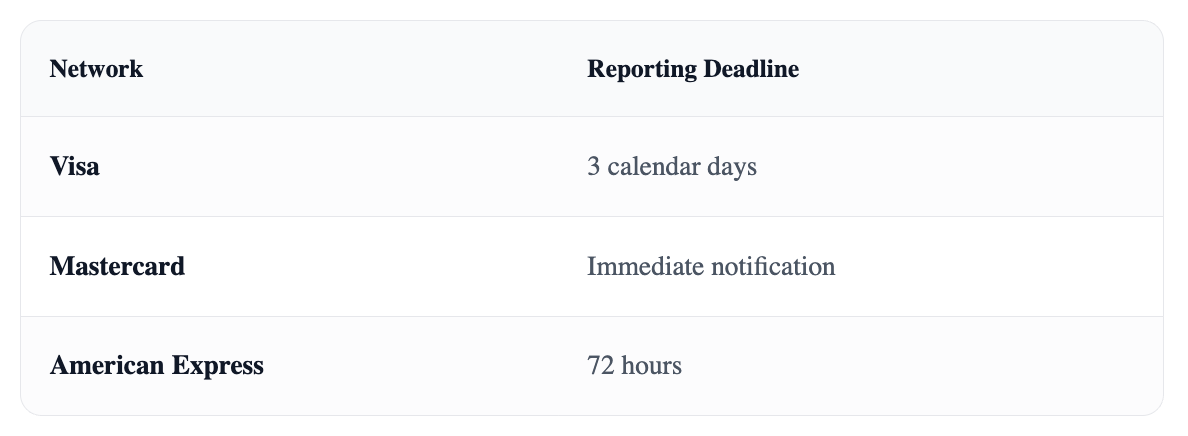
Missing reporting deadlines can eliminate your fraud protection. Your incident response plan must include immediate card deactivation, evidence preservation (do NOT power off compromised systems; volatile memory contains critical forensic data), and pre-assigned team roles.
Post-incident, conduct root cause analysis to close the gap that allowed the fraud. The goal is never to experience the same incident twice.
Stop Reacting to Fraud, Start Preventing It
These 10 practices work together as a system, but implementation often comes down to having the right tools. Traditional bank cards offer zero operational control. Expense platforms miss travel-specific needs. You end up stitching together multiple vendors.
Engine X brings travel booking, corporate cards, and spend management under one roof. Issue unlimited cards with project-level controls. See every transaction as it happens. Earn up to 10% back on travel and 1.5% on everything else1.
Ready to protect your field workforce while earning up to 10% back on every trip? Apply for Engine X and get fraud-proof corporate cards built for distributed teams.
.png)
Frequently Asked Questions
How can virtual cards reduce fraud risk for distributed teams?
Virtual cards generate unique numbers for each transaction or vendor—once used, intercepted numbers become worthless. They offer customizable spending controls, lack physical form (eliminating theft risks), and can be frozen instantly.
For project-based businesses, Engine X lets you issue unlimited virtual cards tied to specific jobs, vendors, or expense types, each with its own spend limits.
What are the key differences in fraud protection between business and consumer cards?
Business cards often lack the federal $50 liability cap that protects consumer cards. However, they provide more oversight tools: real-time alerts, role-based spending limits, and project-specific controls.
Purpose-built corporate charge cards like Engine X integrate with travel and expense platforms for consolidated visibility and policy compliance.
How does real-time transaction monitoring help distributed teams prevent fraud?
Real-time monitoring alerts you to suspicious activities as they happen, not weeks later. You can freeze a card before significant damage occurs.
These systems use AI to analyze transaction data continuously, triggering immediate responses to unexpected charges or location discrepancies.
How can companies train field employees to recognize phishing and BEC threats?
Use mobile-first platforms with bite-sized modules. Focus on phishing characteristics: fraudulent addresses, urgent language, and requests for sensitive information.
Conduct simulated phishing exercises with immediate feedback, and establish clear reporting protocols.
What steps should an incident response protocol include for timely action?
Immediate card deactivation and rapid communication with your issuer to meet reporting deadlines. Preserve evidence by maintaining system integrity. Don't power off compromised systems.
Assign clear team roles and conduct post-incident root cause analysis. Regular rehearsals ensure decisive action.
Engine X Visa® Commercial cards issued by Fifth Third Bank N.A., Member FDIC. Terms and conditions apply. All applications subject to credit approval.
1 Earn up to 10% back in points on qualifying Engine travel purchases. Actual reward rates vary by purchase category and may change. Points have no cash value and are redeemable for rewards through our program. See full rewards terms for details.





.jpg)



.jpg)







![How to Get the Best Hotel Deals and Rewards [Infographic]](https://cdn.prod.website-files.com/66a41388b1be9ba182f1e80c/66a41388b1be9ba182f1f257_Windsor_Hotel_-_in_winter.avif)








